Your deleted commits still have secrets in them.
SecretSweep scans your entire git history for API keys, passwords, and tokens. 130+ detection rules. Matches on supported providers (AWS, GitHub, Stripe, OpenAI, Slack, SendGrid, npm) are verified against the real provider API, so you know whether those leaked keys are still live or already revoked. The ones you thought you removed are still there.
Tested on OWASP WrongSecrets, an intentionally vulnerable project used with permission for security tool testing.
130+ detection rules, covering every provider you actually use.
Built on gitleaks (MIT) with a verification dispatcher that tests matches against the real provider API for seven supported providers. If a supported match returns ACTIVE, the rotation runbook opens immediately. Unsupported matches are flagged for manual review.
ACTIVE / REVOKED verification via their real API, not just regex.Rule source: gitleaks/gitleaks.toml. Secret verification is a Pro feature.
A match is only half the work. The other half is knowing it still works.
Every match runs through the real provider API. You get ACTIVE, REVOKED, or a specific reason the check didn't complete. Active keys stay under monthly re-verification with 30, 60, and 90-day escalations, so nothing rots in a backlog.
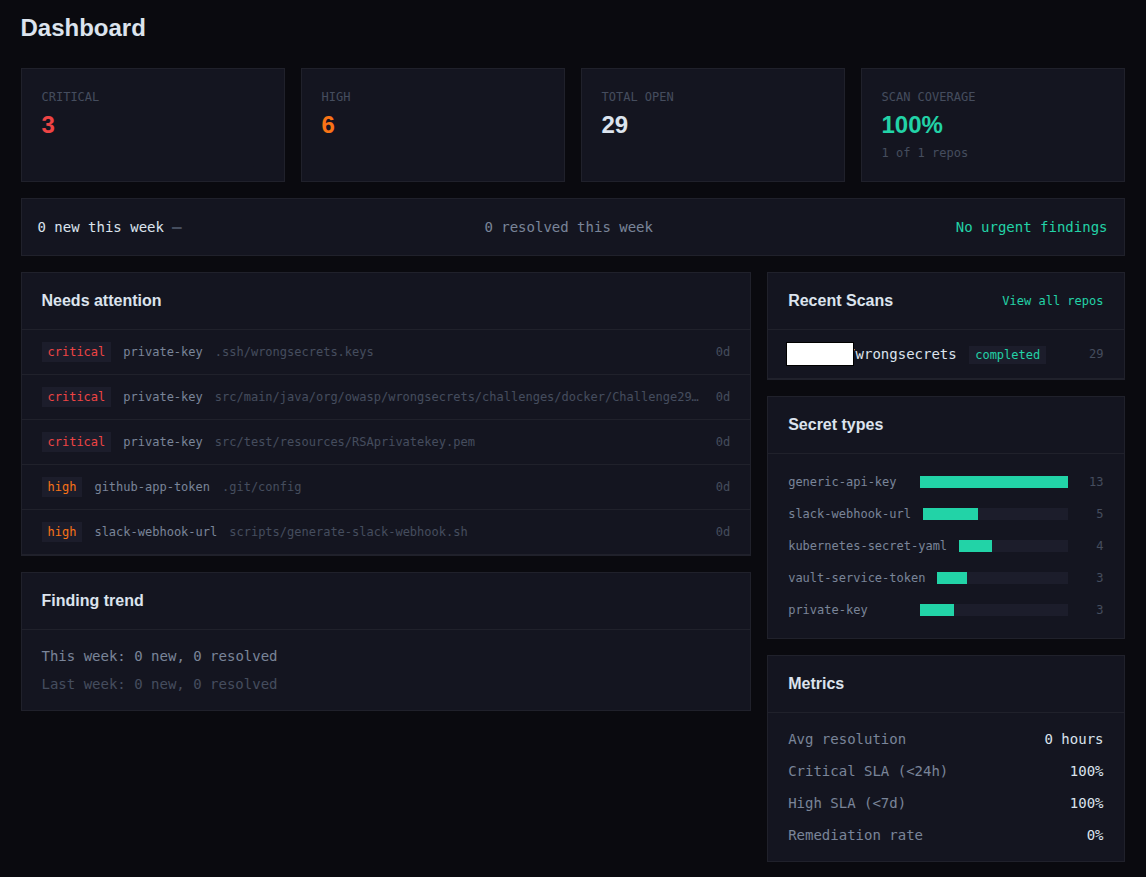
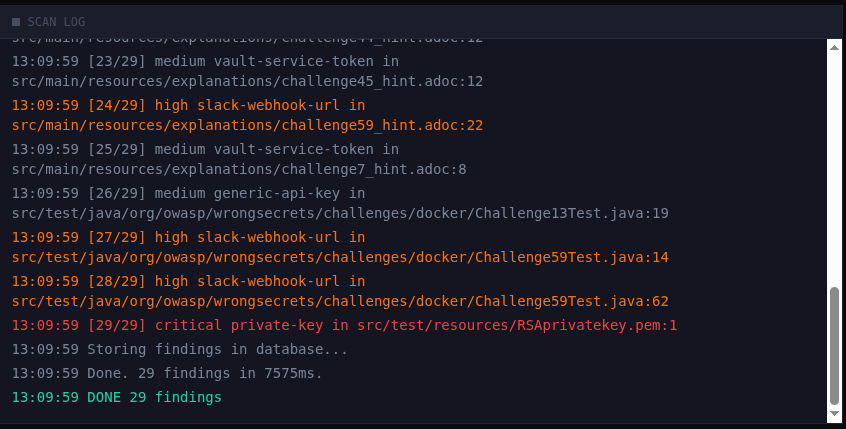
Findings land in the dashboard with severity, source, rotation guidance, and a one-click "Resolve / Ignore / False Positive / Allowlist" flow for every one.
From a live scan of OWASP WrongSecrets.
Six minutes from commit to a compromised account.
Illustrative scenario. Timing is reconstructed from Palo Alto Networks' EleKtra-Leak campaign research, which observed attackers harvesting AWS keys from public GitHub within five minutes of commit. Actual compute charges depend on instance type, duration, and region. Individual outcomes vary.
terraform/main.tfvars.AKIA... is found within the first minute.GetCallerIdentity.Pre-commit hook blocks the push before it leaves your machine, or webhook picks it up within 60 seconds of a push that slipped through. The rotation runbook opens with the finding, with step-by-step revocation steps for 60+ services.
Five minutes to stolen keys. Hours to a five-figure bill.
Three publicly reported incidents. Different companies, different credentials, same mechanism: a key committed to a repo, harvested within minutes, run up until someone noticed. Dollar figures are as reported in each linked source and reflect individual cases, not guaranteed outcomes.
Overnight AWS bill. A developer pushed API keys to a public GitHub repo. Bots picked them up within minutes. By morning, the account had been used to spin up GPU instances for crypto mining, as reported in the source account linked below.
Let's Code Future (2026) →EleKtra-Leak campaign. That's how fast attackers harvest exposed AWS keys from GitHub. 474 crypto miners deployed in a single five-week window.
The Register (2023) →DXC Technology. A contractor's AWS keys were pushed to a public repo. Attackers spun up instances and ran up the bill before anyone noticed.
The Register (2017) →Individual incidents reported in public sources. Outcomes vary by organization, detection speed, and credential scope. Background on overall trends: GitGuardian State of Secrets Sprawl 2024 reports 12.8 million secrets leaked to public GitHub in 2023, with over 90% still active five days later.
Flat pricing. $9 a month for the whole team.
What every other scanner costs for a 5-person team, at published rates:
Competitor pricing reflects publicly published plans at the time of writing. Vendors update their pricing regularly; verify current prices on each vendor's own website before relying on them for purchasing decisions.
Three tiers. None priced per seat.
The free tier is the trial. No credit card, no time limit. When you outgrow 2 repos, Pro is $9 a month for everyone on your team.
- 2 repositories
- 25 scans per month
- Full git history, every branch
- 60+ rotation runbooks
- On-demand scanning
- 50 repositories, GitLab + Bitbucket
- Live secret verification (ACTIVE / REVOKED)
- Monthly re-verification with 30/60/90 day escalation
- Auto-scan on every push
- Pre-commit CLI and CSV/JSON export
- Finding resolution workflow (Resolve, Ignore, False Positive, Reopen) with audit trail
- Custom ignore rules and allowlist
- Unlimited repositories
- CI/CD log scanning (GitHub Actions)
- Scheduled scans (daily or weekly)
- MTTR, SLA compliance, remediation rate
- Resolution velocity dashboards
- Everything in Pro
/billing, one click, no email to sales.
Invoices auto-email. Tax receipts on request. Cancel anytime, paid period stays active until it ends.
Federal supply chain requirements now expect automated secrets scanning.
If you ship software to the government, or work with organizations that do, demonstrating secrets management practices can be part of your security review. Power produces scan histories and audit trails that can support your internal compliance work.
Directed NIST to develop secure software development guidance, which became NIST SP 800-218. OMB Memorandum M-22-18 then required federal agencies to obtain vendor self-attestations that practices align with that guidance.
Describes secure development practices including automated vulnerability detection, which secrets scanning supports. Federal agencies reference SSDF in procurement.
Requires defense contractors to protect Controlled Unclassified Information. A leaked AWS key in a repo with CUI access is a finding.
Requires logical access security over protected information assets, including credential management. Automated scanning provides concrete evidence for auditors evaluating your controls.
SecretSweep is a scanning tool, not a compliance authority. References to EO 14028, NIST SP 800-218, CMMC, and SOC 2 describe publicly available regulatory requirements and do not imply endorsement by or affiliation with any government agency. Organizations should consult qualified auditors and legal counsel for formal compliance assessments.
Questions, answered.
$95/mo at published rates. SecretSweep Pro is $9/mo flat, works with any GitHub plan, and includes GitLab + Bitbucket.30/60/90 days. Nothing rots in a backlog.Run one scan. See what your git history is still carrying.
Free for 2 repos, no card. If the free tier catches one live key, it paid for itself at whatever your hourly rate is.